5 TIPS FOR IT SECURITY IN HOME OFFICE
Exit restrictions, social distancing, home office – many of us are currently working from home and are therefore mostly alone. But are we really alone, socially distant, and thus safe?
No. Quite the opposite: We are all exposed these days – to cyber attackers!
Very few of us regularly work in home office.
Thus, the spontaneous solutions that many currently use do not always meet the IT security requirements that we would normally demand of them.
This opens many doors for those who are looking for information and data from our companies.
So, what can we do in the short term to protect ourselves in the current situation?
The German Federal Cyber Security Authority (BSI) recommends the following
“Top 5 for IT security in home office”:
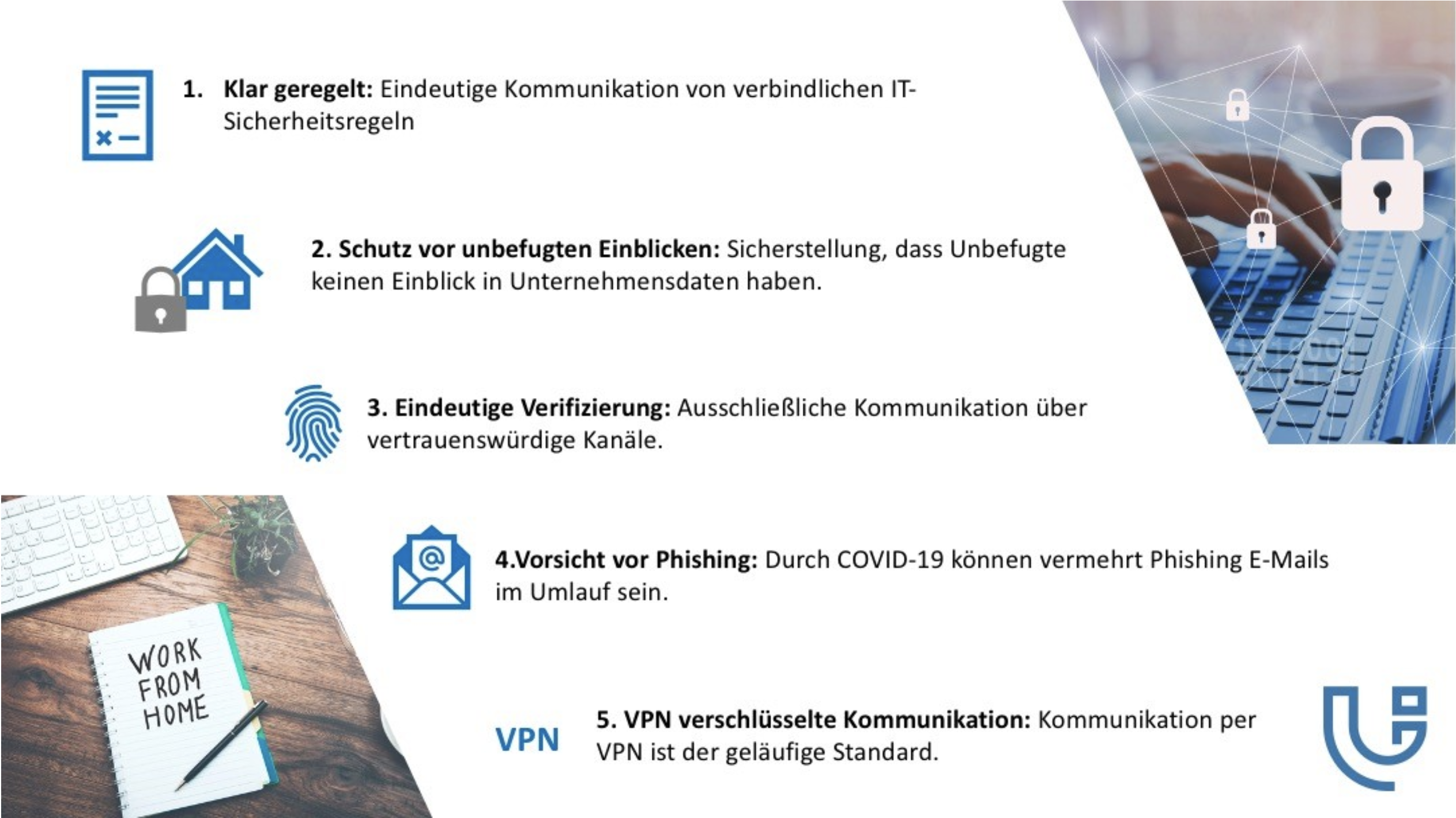
Clearly regulated: Unambiguous and binding regulations on IT security and the security of data in paper form are essential and should be communicated clearly and in writing to everyone involved.
There is nothing to see here: Home office should be as close to the company office as possible in terms of security.
Lock your devices when you are not using them.
Close doors when you leave the workplace.
Make sure that third parties cannot look at your screen through visible or open windows.
Clear verification: Use only trustworthy communication channels.
Beware of phishing: Many attackers are taking advantage of the current situation and could try to gain access to sensitive data by exploiting fears, obtaining information about remote access or resetting passwords.
VPN: If possible, you should only access your institution’s resources via secure communication channels.
One possibility for this is cryptographically secured virtual private networks (VPN).
Learn more about IT security with University4Industry.
Here you will find more information.
Or simply contact us at: info@university4industry.com
More information and links to further resources can be found on the BSI website.